Multi-Layered, Zero Trust Cybersecurity
Confidential & Resilient
Security across the hardware, firmware, software, and network layers reduces physical and digital attack surface.
"Always-On" Protections
Our hardware operates as if a hacker has already gained access, helping to thwart unknown vulnerabilities.
From Chip To Edge
Hardware- and software-based cybersecurity provided by our global technology partnership ecosystem.
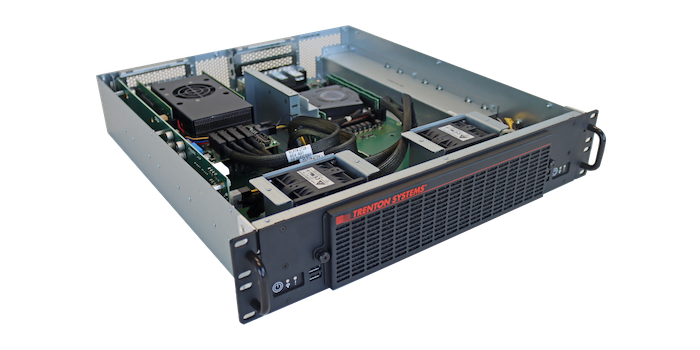
Trenton Systems' Fortified Security Layers
A Comprehensive Approach to Protecting Data-at-Rest, In-Transit, and In-Use. Technologies provided by our global partnership ecosystem.
Hardware Layer
Our hardware solutions are designed with built-in security features to protect against physical and hardware-based attacks.
From secure boot mechanisms to hardware encryption engines, we implement robust security measures at the hardware level to safeguard critical data.
*FIPS 140-2/3 certified, NIAP-listed, self-encrypting NVMe/SATA/SAS SSDs available upon request.
Firmware Layer
We employ rigorous firmware validation and integrity checks to detect and mitigate potential threats.
Additionally, we perform continuous firmware updates and patches, and customize the BIOS source code to ensure that our systems remain resilient against emerging threats.
Software Layer
Our software solutions undergo thorough security testing and code reviews to identify and address potential vulnerabilities.
We also partner with leading cybersecurity firms to integrate advanced security solutions into our software stack, enhancing protection against malware, ransomware, and other cyberthreats.
Network Layer
We implement robust network security measures, including firewalls, intrusion detection/prevention systems (IDS/IPS), and virtual private networks (VPNs), to safeguard data-in-transit.
Additionally, we leverage encryption protocols such as SSL/TLS to ensure secure communication channels across networks.
Trenton Systems' Latest Cybersecurity Solution
Next-Gen Hardware Isolation Platform
Unlock secure data transfer between classified networks with Trenton Systems' advanced hardware isolation platform.
Seamlessly share sensitive information across varying security levels, ensuring compliance and bolstering collaboration while safeguarding data integrity and critical workloads.
Strengthening Security Together
Robust cybersecurity across a system's entire infrastructure against a wide range of threats to protect the confidentiality, availability, and integrity of critical data when it matters most.

/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)