What are Neural Networks?
by Christopher Trick on Mar 30, 2022 4:36:35 PM
Artificial intelligence has three subfields that help it equip high-performance computers with powers that match and exceed human abilities. In this blog, you'll learn more about how the second AI subfield, neural networks, helps HPCs analyze data to increase situational awareness and …
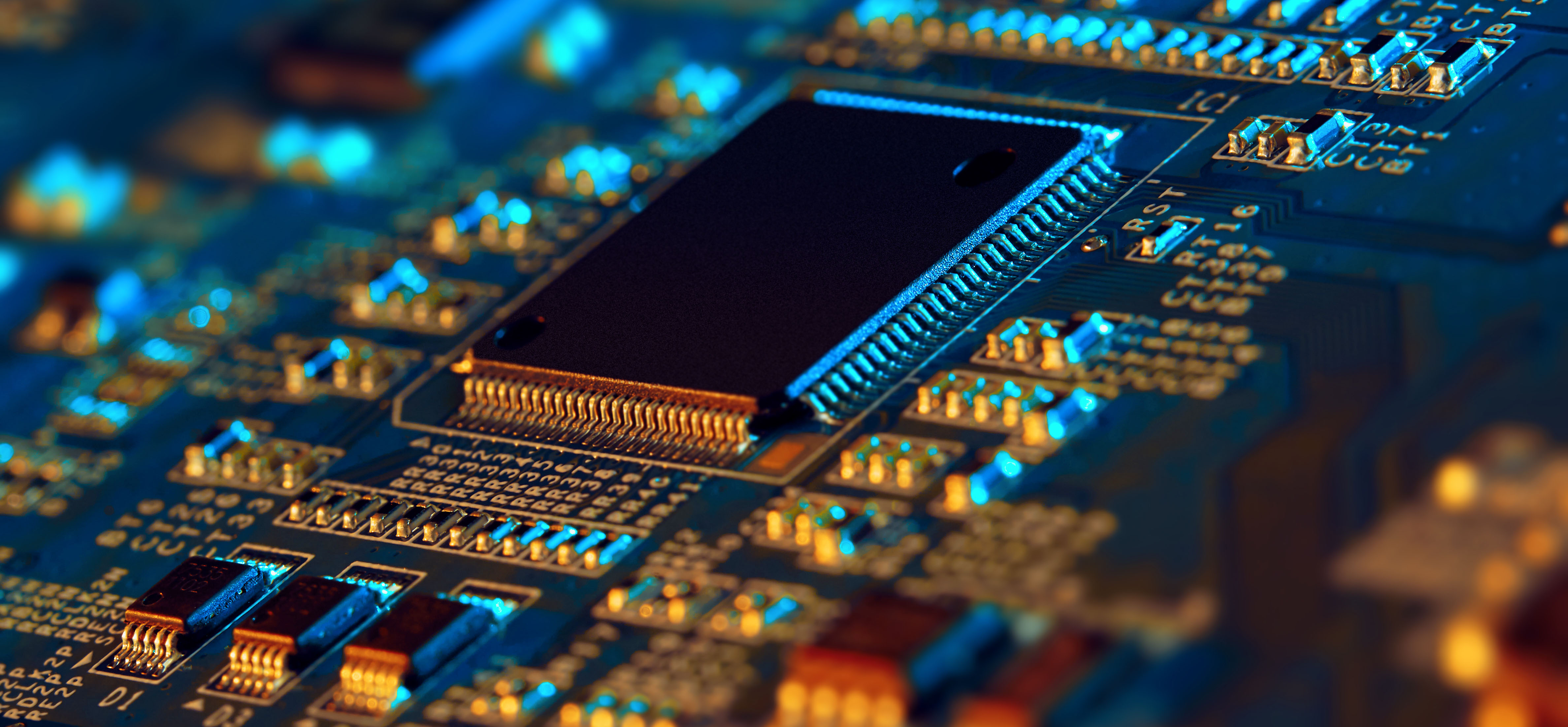
Top Cybersecurity Technologies for 2023
by Christopher Trick on Mar 23, 2022 9:00:00 AM
As our world becomes increasingly digitized, protecting critical mission systems across the hardware, firmware, and software layer stack is vital. In this blog, you'll learn about the technologies necessary to secure your high-performance computing solutions (HPCs) against unauthorize …
How to Secure Your Operating System (OS)
by Christopher Trick on Mar 22, 2022 9:13:31 AM
Failure to protect your operating system, perhaps the most important software on a computer, can lead to various kinds of cyberattacks, impeding performance and compromising critical data. In this blog, you'll learn how to secure your OS in order to protect its confidentiality, functi …
What is Full-Disk Encryption (FDE)?
by Christopher Trick on Mar 22, 2022 9:12:50 AM
Disks and drives store massive amounts of critical data, making their security against cybercriminals a top priority. In this blog, you'll learn what full-disk encryption (FDE) is and why it is critical to the protection of an entire disk volume and all files on a drive against unauth …
What is IPMI? A Guide to Intelligent Platform Management Interface
by Christopher Trick on Mar 21, 2022 11:03:45 AM
A BMC (Baseboard Management Controller), which is an embedded computer that can access and control all of a server's resources, uses remote management capabilities to increase efficiency but can be hacked at any time, posing security risks. In this blog, you'll learn what IPMI (Intell …
What are Pre-Boot and Post-Boot Authentication?
by Christopher Trick on Mar 18, 2022 10:35:59 AM
As cyberattacks become more advanced, traditional safeguards and authentication measures like usernames and passwords provide operating systems with less protection. In this blog, you'll learn more about what pre-boot and post-boot authentication are and their role in protecting criti …
What is Intel TME (Total Memory Encryption)?
by Christopher Trick on Mar 17, 2022 1:57:36 PM
Memory attacks have quietly emerged as a new class of hacking techniques to undermine conventional security measures, posing a threat to all data that passes through a system. In this blog, you'll learn how Intel TME (Total Memory Encryption) acts as a necessary safeguard for protecti …
Trenton Systems expands with new headquarters in Duluth, GA
by Christopher Trick on Mar 10, 2022 3:47:22 PM
The Ultimate Guide to Hypervisors: Definitions, Types, and Security
by Christopher Trick on Mar 9, 2022 9:00:00 AM
As the world become increasingly digitized through the use of computers, cloud services, and other virtual tools, organizations and individuals have become more vulnerable to data breaches. In this blog, you'll learn about hypervisors and why their security is critical to preserving d …
What is Secure Flash?
by Christopher Trick on Mar 8, 2022 9:00:00 AM
As cyberattacks become more sophisticated, software-based security solutions, though inexpensive, are proving to be relatively ineffective in the face of more advanced threats. In this blog, you'll learn about how secure flash helps protect critical data from theft, manipulation, and …
How to Secure Your BIOS
by Christopher Trick on Mar 7, 2022 3:50:02 PM
BIOS security is integral to the protection of critical information and ensuring unauthorized personnel cannot access or control your system. In this blog, you'll learn three ways to secure your BIOS to ensure your system is fully protected across the hardware, firmware, and software …
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)