Share this
Hacked Hardware, Spy Chips: How to Help Secure Your Servers
by Yazz Krdzalic on Oct 9, 2018 9:31:28 AM
In this blog I'll share with you a step-by-step guideline on how to keep your servers protected from possible hardware hacks.
I will also summarize Bloomberg's post that started the conversation about hardware cybersecurity and explain how hacked hardware is a real threat with actual customer use cases.
Let's begin.

Bloomberg's Unforgettable Post
I doubt that you haven't heard about it by now, but just in case:
Chinese spies manage to pull off the biggest hardware hack in history using tiny microchips to infiltrate almost 30 U.S. companies, including Amazon and Apple, and compromising America's supply chain. This report, published by Bloomberg Businessweek on October 4, 2018, sent a massive shockwave through the tech world.
Moments later, the news reach all corners of the earth.
The aftermath?
Of those mentioned in the article, stocks simply plummeted, many others are up in arms about the possible implications, and interestingly enough, all during National Cybersecurity Awareness Month.
The Day After
24 hours after the initial shock took the internet by storm, we seem to have a house divided: the believers and the skeptics.
Let's start with the Skeptics
These are individuals who doubt every claim or dismiss the story altogether. Valid proof is the theme behind their arguments. After all, it's just impossible for U.S. companies of that size to purchase hacked hardware implanted with spy chips.
By Chinese spies?
...AND it goes unnoticed for multiple years?
I mean, really? Who'd believe any of that?
Let's meet the Believers
Labeled as conspiracy theorists, panic-inducing social media trolls, or simply put: liars - by every skeptic out there.
[I've had my fair share of insults for simply sharing the article on social media]
The theme here: Nothing is impossible.
Why?
Here's a snip from the article to think twice about the realm of possibility:
"The security of the global technology supply chain had been compromised, even if consumers and most companies didn’t know it yet."
Need another?
"The companies’ denials are countered by six current and former senior national security officials, who—in conversations that began during the Obama administration and continued under the Trump administration—detailed the discovery of the chips and the government’s investigation."
The article lists numerous others - highly recommend you read it for yourself to form your own opinion.
Who's right and who's wrong?
I don't think that's the question we need to be asking ourselves.
No matter which side of the fence you're on, one thing is crystal clear - it IS possible and if there is ANY truth to this story - the problem of hacked hardware is a matter of national security.
Our personal data is at stake.
The government's sensitive files could be compromised.
We could all be at great risk if the information landed in the wrong hands.
The question we need to ask ourselves instead is...
How do we prevent The Big Hack from happening (again)?
In our world of rugged high-performance computing, hardware hacks are a real concern and a very real threat. For us and for our customers.
How real?
Let me answer that with a use case. [Client's names will not be listed for confidentiality purposes]
Customer A purchases numerous systems on an annual basis. These systems hold sensitive data that cannot be compromised under any circumstances. The client has implemented numerous processes to secure the data no matter where it is stored physically or what state it is in. These processes are intricate and involved, both from a logistics as well as a systems infrastructure standpoint. Numerous software applications are installed to protect the front-end from being attacked - but the hardware is still at risk. The customer's rugged computers are exposed to unauthorized parties and thus placing the physical servers/systems at risk of an intrusion - hardware side. To ensure their utmost security, they rely on us to design, manufacture, assemble, and integrate their newly built systems with anti-hardware hacking guidelines already in place. This protects them from any unwanted party gaining access to the system via a physical connection (think LAN ports, USBs, etc.) or foreign chip on the hardware (the case in Bloomberg's article).
How does this really help you?
Set expectations for your Manufacturer - on first contact
When you design, manufacture, assemble, and support the very hardware your customers depend on, it's vital - scratch that - it is a MUST to understand possible backdoors a hardware hacker would infiltrate to gain access to an otherwise protected system.
This is no arena for cutting corners or taking shortcuts.
Ensuring absolute security is P1.
End of story.
Your manufacturer needs to understand these threats and protect you from a possible hardware hack in the future.
How do you choose the right computer manufacturer?
Start with a US-made manufacturer.
I don't mean someone who is physically located in the US yet offshores all other aspects of the business.
When I say US-made, I mean the entire process is done state-side.
Here's what I mean:
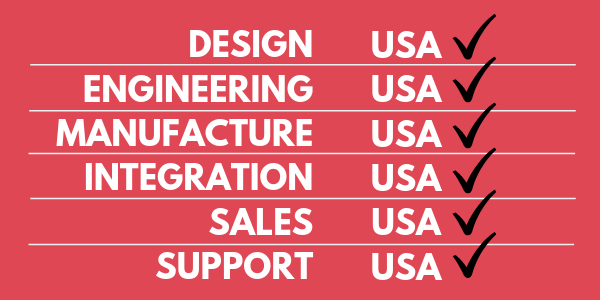
Some manufacturers hide in the details.
They'll make the rugged chassis in the USA but integrate a 3rd party motherboard, which may come from other parts of the world that does not have strict rules & regulations into the manufacture/assembly process.
Others only have a Sales Team that is state-side, while all product/service related matters are offshore.
This can greatly impact your system security and put you and your customers at risk of a hardware hack.
The best way to filter your list of manufacturers is by asking the right questions up front.
What questions should you ask the manufacturer to determine if that's the right choice for you?
This is no small task. Keep in mind, no matter which manufacturer you choose, you are looking at a long-term relationship - few years at least.
These sorts of partnerships require you to think long-term strategy and total cost of ownership. A significant amount of your time, money, and resources will be spent - choose wisely and remember to weigh all of your options.
As promised, here are some questions to help you screen your list of manufacturers:
- Who designs your bare boards?
- [if not done by manufacturer] Where is this company located?
- Do you have an engineering team in-house?
- Do you have mechanical and electrical engineers that work on your products in-house?
- What steps do you take to ensure your products are not prone to hardware hacks?
- Can you disable the BMC if I needed you to? How would you do so? Are your engineers on this sort of task or do you outsource?
- Is your facility ITAR certified?
- Do you outsource any component-related work to 3rd party vendors?
- Who manufactures your products?
- Who integrates your products?
- Is your Sales Team state-side as well or do you have them all over the globe?
- Is your Support Team based in the USA or do you offshore these services?
- [If Support Team is US-based] Is your support team in the same building as your Engineers or do you have another company handle these requests?
Don't be alarmed if these questions eliminate a large number of manufacturers from your list. At the end of the day, you need to choose the security of your hardware and ultimately your computer systems above all else.
I am already in a long-term relationship with the incumbent, now what?
Chances are, you already have someone providing your high-performance computers. Possibly even, they've been your go-to for years.
Still, you can't shy away from asking them the same questions above; and let it not surprise you if they don't meet the qualifications either.
Breaking up is never easy. What should you do if you need to jump ship?
If you have to jump ship, then take some precautions and let the new manufacturer of choice absorb some of your pain points. This will ease the transition and provide smooth sailing henceforth.
Ask the new manufacturer about their integration capabilities. Describe your system in detail, give as much info as you can, and list your need-to and would-like-to haves - a top tier manufacturer will take both into consideration. After all, they should be delighted to showcase their products and services to you.
[first impressions last forever]
A lot of your worries should be thoroughly answered by their team. Not only Sales, but Engineering, Production, and all the other aspects that are of concern to you. Make sure to find out how their teams interact with each other, as that is usually a great indicator of how they will interact with you.
Send e-mails, start chats, give them a call - whatever it takes to measure their response rate as it is going to be vital during onboarding.
Final thoughts & summary
At the end of the day, your choices about which products you purchase and whom you choose to do business with is going to impact how prone your hardware is to hacks. If you don't do your homework, you are only hurting yourself.
The comfort of staying with the incumbent, no matter the practices in place, can cost you tremendously in the long-run. On the other hand, moving to a new manufacturer might be much easier than you think.
Asking the right questions at the right time will filter out those who hide behind every asterisk on their datasheets and web pages vs. those who stand by what they say.
Know what you want and what you need and don't be afraid to demand it - those willing to fight for your business with a passion to solve your problems before they arise are your true contenders.
Evaluate their products, services, and if you have the chance, meet in person.
If there's one thing I'd like you to take away from this post it's this:
Hacked hardware is real. It happens more often than you think and it can wreak havoc on your infrastructure if it is compromised. Don't ignore it. Take the necessary steps to ensure you're protected and have the right resources in place that fight the problem before it occurs.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)
No Comments Yet
Let us know what you think