Share this
Private 5G Networks for Mission Critical Communications
by Philippe Weber on May 2, 2024 10:59:58 AM

Introduction
In the rapidly evolving landscape of telecommunications, private 5G tactical wireless networks are emerging as a transformative force, particularly in the realm of mission-critical communications. These networks, designed with robustness and reliability to withstand challenging environments, are poised to revolutionize how critical information is exchanged in high-stakes situations.
5G wireless technology, with its high-speed data transmission, low latency, and ability to connect a vast number of devices simultaneously, offers unprecedented opportunities for enhancing tactical communications. From military operations and emergency response to disaster management and public safety, 5G tactical networks are set to play a pivotal role.
This new generation of wireless technology goes beyond providing faster speeds. It brings about a paradigm shift in network architecture, offering enhanced security, resilience, reduced footprint, adaptation to environmentally challenged environments and interoperability. These features are crucial for mission-critical communications, where the stakes are high, and failure is not an option.
This article describes how 5G technology can be deployed to provide highly secure, private 5G tactical networks for Mission Critical Communication, and some of the technologies that enable this deployment.
Open RAN and the disaggregation of the Base Station
In the past, Baseband Units (BBUs) at the base of radio towers were monolithic functions based on proprietary equipment. The ORAN (Open RAN) concept disaggregates them into scalable, interoperable, cost-effective functions based on open interfaces and available from multiple suppliers. In addition, software-based RAN, also called vRAN for Virtualized Radio Access Network, allows to run them on general purpose computers. This concept is known as Network Functions Virtualization (NFV).

ORAN components
As shown on the figure above, 3GPP (3rd generation partnership project) release 15 defines the disaggregated logical entities as:
- CU: Centralized Unit.
- DU: Distributed Unit.
- RU: Remote Radio Unit
Split options 7.2x and 2 define the interfaces between all components. Once grouped, components form the gNB (Next generation Node B), the 5G “base station”.
Low-latency, high priority communications
Compared to 4G/LTE, a key improvement of 5G is its capacity to ‘slice’ a physical network into several virtual networks, with the possibility to assign dynamic priorities, resources, or specific Quality of Service (QoS) parameters to each network.
Additionally, its URLLC technology – for ultra-reliable low latency communications – allows end-to-end latency lower than 1ms and reliability of more than 99.999 %.
For example, a private 5G network deployed in a military post, could in normal operation mode allows high-resolution video calls to be placed, but during an enemy attack, absolute priority and minimum latency would be granted to real-time communication with defensive weapon systems.
What is a private 5G network?
Most people are familiar with public 4G/LTE or 5G networks, as provided by commercial operators like AT&T, T-Mobile, Orange, etc. An independent, private 5G network will offer the same functionalities, but will cover only specific buildings or terrain zones, and will be entirely managed by the user organization. It may or may not be connected to the public Internet. Because it is privately managed, a private network can provide the levels of robustness, flexibility and security required in Mission Critical Communication.
Like on a public network, authorized 5G User Equipment (UE), such as smartphones, tables, or IoT sensors, will be registered on the network via SIM cards or eSIMs provided by the private operator.
One can compare a private 5G network to a bubble, inside which 5G communications are enabled for all authorized users, and that can geographically move as gNB stations and the 5Gcore processing units move.
Wireless access backhaul
Wireless access backhaul refers to the method of connecting the network infrastructure of a wireless communication system using a wireless connection instead of a wired connection. Base stations are connected to the core network wirelessly, usually using radio, or satellite communication (SATCOM) technologies.
Wireless access backhaul can be useful in situations where laying physical cables is difficult, costly, or impractical, such as in rural or remote areas. It can also provide a temporary solution in disaster or emergency situations, military theaters of operations where wired connections may be unavailable.
A fully standalone 5G network will have no wired or wireless access backhaul at all, and still will provide all the functions of a public network.
Small-footprint private 5G network
The figure below shows a small-footprint, integrated, cost-effective, ruggedized 5G gNB node running on a general-purpose server, like implemented on the Trenton System IES.5G product. It comprises 3 hardware elements, an outdoor Radio Unit, a rugged server and a GNSS satellite antenna. Here, the RU connects to the server through a 25gbs fiber interface, the antenna provides source for the PTP grandmaster clock. An Intel E810 NIC card installed in the server allows direct connection to the server from the GNSS antenna or from a PTP clock source, as well as high speed connection to the RU and the private, local or public network.
The server runs DU and CU functions, as well as 5G core functions. For that purpose, it will integrate software packages from suppliers like GCX (GXC Onyx) and Intel (FlexRAN).
Because of the relatively small footprint of the software functions above, the server can take benefit of its multi-core architecture and expansion capabilities, to run in parallel general purpose user functions such as database and storage, local cloud, encryption/decryption, signal processing and routing to other links such as SATCOM.

The architecture is inherently scalable and modular and can easily extend and adapt to changing environments:
- Additional RUs, indoor or outdoor, meshed or not, via fronthaul switches
- High power RUs for extended coverage
- Different 5G frequency bands, aligned with international regulations
- Additional processing or storage capabilities
- GPU cards for AI/ML/DL or signal processing
- 5G Hardware accelerators
- Redundant operation and additional nodes
- Zscaler Zero-trust cybersecurity platform to provide robust security capabilities
Used in mobility, this architecture largely reduces physical footprint, as well as Electro-Magnetic presence, which shows very valuable for militaries. The entire system is easily transportable in a transit case or on a ground vehicle.
Intel’s contribution to 5G networks
I’d like to highlight the many Intel software and hardware products that support vRAN integration and scalability and that are or can be integrated in the example above:
- Software stack:
o FlexRAN (see https://www.trentonsystems.com/en-us/resource-hub/blog/what-is-intel-flexran)
- PCIe cards:
o E810 PCIe Network Interface Controller card with auxiliary PTP, GNNS inputs
o ACC100 forward error correction (FEC) accelerator
- Processor instructions:
o AVX-512 SIMD instructions for vector processing, vRAN level 1
o vRAN Boost instructions in Xeon SP Gen 4 processors
o QAT crypto accelerator in Xeon SP Gen 4/5 processors or as a separate hardware accelerator
Private 5G networks in military environments
The figure below shows an example deployment of multiple 5G “bubbles” in a military environment, and the connection of all network objects via 5G, SATCOM backhaul or legacy radio links.
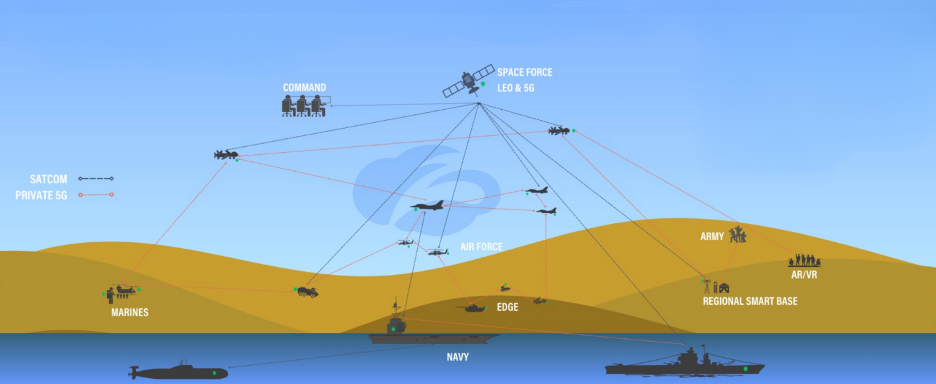
A typical implementation of a private 5G network in a military Mobile Command Post could be made of:
- 2 network access points (RU) configured for redundant operation and connected to the server
- Rugged Server on a vehicle or on the ground in a transit case
- SATCOM connection for wireless access backhaul
- UAVs flying over scene and possibly providing aerial signal relay
- Mesh networking (5G relays on ground or on aerial relays) for the connection of multiple, remote, moving vehicles or soldiers
- The IEEE 1588 PTP source can be GNSS satellites, or a local Cesium-based high precision clock if utilizing satellites represents a security issue.
- User Equipment includes smartphones, tablets, 5G-enabled augmented reality (AR) devices, as well as 5G-enabled Unattended Ground Sensors (UGS) or cameras
Final thoughts
The advent of modern 5G communication, particularly when implemented in private 5G networks, has opened up a world of possibilities. It has become a game-changer in the realm of digital communication, offering high-speed, low-latency, cost-effective, and secure communication solutions. This is particularly beneficial for mission-critical applications where reliability, speed, and security are paramount. The transformative potential of private 5G networks is immense, and as its technology continues to evolve, it will undoubtedly continue to revolutionize the way we communicate, work, and live.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)
No Comments Yet
Let us know what you think