Share this
Security for USB Ports: Why Do Computer Manufacturers Disable Them?
by Brett Daniel on Feb 19, 2021 10:02:44 AM
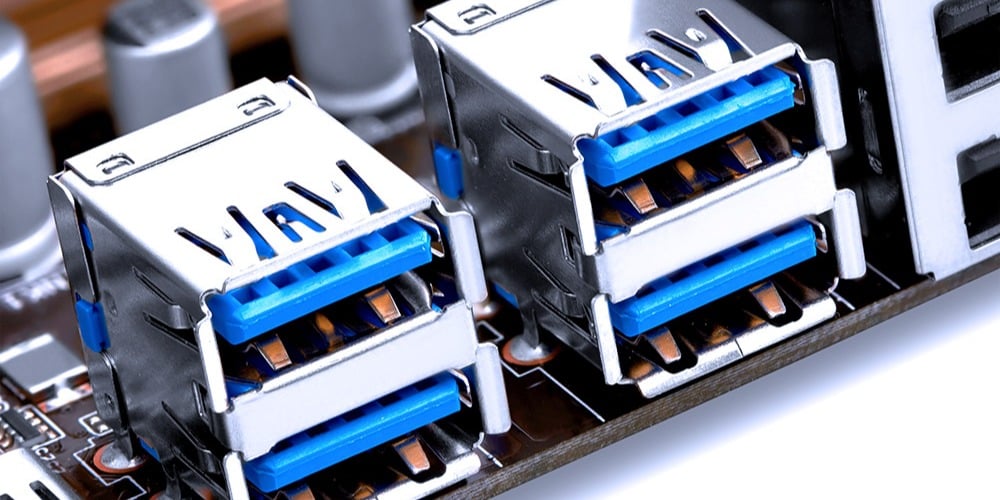
Photo: Like other system hardware, USB ports need a bit of tender, loving protection.
Table of Contents
- Why do companies disable the USB ports on their computers?
- How do hackers target USB ports?
- How can I protect my USB ports?
There are a lot of security measures you can take to protect your high-performance computer (HPC), from implementing FIPS self-encrypting drives (SEDs) to installing comprehensive security suites and so on.
But cyberattackers are beginning to focus more on attacks, whether in-person or originating from supply chain infiltration, that target a system's hardware. One of these attack methods involves USB ports, which some security-conscious computer manufacturers, like Trenton Systems, disable to protect their customers.
In this blog post, we'll explain why disabling USB ports makes sense, how cyberattackers target USB ports, and what you can do to protect them.
Why do companies disable the USB ports on their computers?
Computer manufacturers sometimes disable Universal Serial Bus (USB) ports as boot sources to protect end customers from a USB cyberattack.
Disabling USB ports at boot time is achieved when firmware designers set USB disablement parameters within a system's Basic Input Output System (BIOS).
The keywords here are "at boot time," meaning that once a user accesses a computer's operating system (OS), the USB ports should become fully functional again. In other words, the disablement is not permanent; the USB ports are only disabled at boot time.
If a computer manufacturer disables a system's USB ports, it's usually because the customer has requested this temporary disablement as an added security feature, although a manufacturer may also recommend this option to highly security-conscious customers, anyway.
But how does disabling USB ports benefit security?
Not allowing USB ports to become functional at boot time keeps computers from running infected operating systems and Unified Extensible Firmware Interface (UEFI) BIOS executables written to contaminated USB flash drives.
That's a longwinded way of saying that your USB ports would be unable to read potentially infected flash drive files. But we bet you're wondering how an infected flash drive could ever make its way into your secure computer.

Photo: Cyberattackers can successfully hack your system using its USB ports in a few different ways.
How do hackers target USB ports?
Cyberattackers use two common methods to attack USB ports: the Direct Insertion Method and the Human Curiosity Method. There's also a less common method, which involves manipulating the baseboard management controller (BMC).
We'll let Chris Sheppard, software engineer at Trenton Systems, explain.
The Direct Insertion Method
Many HPCs give boot priority to USB drives, not hard disk drives (HDDs) and solid-state drives (SSDs). So, if a hacker wanted to, say, engage in a bit of corporate or government espionage, they could just insert a contaminated USB stick into a valuable system housing lots of private data, reboot or wait for a user to reboot, and watch Rome fall.
If you're a hacker, you can take advantage of USB boot priority, and you can stick a flash drive in, maybe install something that, when a user reboots the computer again, even after the hacker removes the USB stick, the OS that's in there looks like it's running normally, but it's actually contaminated, and your data is being stolen, altered, deleted, or what have you.
 Chris Sheppard, Software Engineer, Trenton Systems
Chris Sheppard, Software Engineer, Trenton Systems
The Human Curiosity Method
But even once USB ports become functional after the boot process, hackers can still use them to infect your system. The scariest part is that they can get you to infect it for them.
So, there's the hacker who could sneak in and insert a USB drive into your computer, sure, but what's even more common is a hacker that leaves a bunch of USBs in a parking lot of the place they're attacking. This tactic leverages human curiosity because employees want to know what's on the drives, so they pick them up, stick them in their computers, and they're toast because Windows and other operating systems will scan the drive contents automatically. It sounds ridiculous, but this is a prevalent and successful way of attacking banks and such.
The Baseboard Management Controller (BMC) Method
A less common way that cyberattackers target USB ports is by manipulating a computer's baseboard management controller (BMC).
If you have a BMC, you typically run it really tight and make sure that it can't speak to the internet, but imagine if you made a mistake and that someone was able to get ahold of your BMC. Well, a really well-designed BMC can virtually mount a USB stick.
So, if you're at your desk, and you have a USB flash drive in a USB port, but you tell the computer to mount the flash drive to another computer virtually, the BMC would do it, and this is one way that you could perform a USB booting attack without physical access. That would be very clever and harder to pull off because IT is very protective of the BMC.

Photo: If you like it, then you should have put a lock on it.
How can I protect my USB ports?
One of the best ways to safeguard your USB ports is to work with a manufacturer on disabling all or certain USB ports upon boot. Companies who customize the BIOS, like Trenton Systems, can do this for you if you ask.
Some customers want all USB ports disabled at boot, and others only want specific ports disabled. For example, the USB ports located at the rear of a system might remain enabled because it would take hackers more time and effort to hack these without getting caught. Or a customer might keep a random, difficult-to-see-and-access USB port active in case they ever need to boot a recovery drive.
Another great way to protect your USB ports is to install literal doors and locks on them. That way, you remain in full control of how, when, and what drives go in and out of your ports. Now, if a hacker can break these physical barriers without getting caught, they can still hack your system using the boot method if your ports aren't disabled. So, we highly recommend implementing the boot disablement option as well.
At Trenton Systems, because we work with BIOS source code and thus have the ability to customize it, we can add BIOS security features that fit your unique needs. These features include setting all of certain USB ports as disabled at boot. Not all of our systems have this feature now, but we can add it if you request it. We will also be offering Intel Platform Firmware Resilience (PFR) on our upcoming servers and workstations.
If you're interested in USB port disablement and a custom BIOS for your secure, high-performance computing solution, don't hesitate to ask. We'll work with you every step of the way.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)
No Comments Yet
Let us know what you think